In adtech, we have to confront a lot of pitfalls. As we grow our technology, fraudsters grow theirs to spam the Internet. But, in the end, publishers are held liable by the readers and advertisers. Forced redirect ads are on their way to make the condition even worse. So, here’s the guide to deal with it.
Before we start with anything, let’s have a quick refresh of the basics.
Table of Contents
What are ‘Forced Redirect Ads’?
When a user tries to access a webpage (known), he/she will be redirected to the unknown site(s) and infected with malware or shown a fake ad to collect personal information. Know more here about Ad Fraud.
“Malware accounts for .5% of all ads served, but can vary by a factor of five during an outbreak of forced redirect ads.”
-Louis-David Mangin, CEO, Confiant (Src)

The redirect could be via links, disturbing pop-ups, or through a webpage overloaded with display ads. In fact, fraudsters develop trust with publishers by posing as a legitimate ad network for a certain period of time and then start dropping in malware through ad creatives in order to forcibly redirect destinations for the users.
“This comes up every year – and this is the worst-case [we’ve seen in] the past several years”
– Dave Pond, GM of Display and Programmatic, Vox Media.
How is it done?
There are generally three primary ways to insert forced redirect ads on the website or web path:
1. At ad request level
2. At post-click level
3. Implementing malicious code
At ad request Level
An ad request always goes through a number of different levels such as third parties ad networks, SSP, etc. before reaching the buyers. During this journey from start to end of an ad request, the bad actor infuses the code that sends the user to an unwanted destination.
At Post Click Level
Whenever a user clicks on an ad, the click request is seized and the user is redirected to an unintended destination.
Malicious Code Implementation
This is one of the most widespread reasons for forced redirects. While creating the ad inventories or designing an ad creative, the malicious code is implanted. Its effect can be seen only when an ad appears and gets clicked.
For instance, last year Vogue came to know that its readers are being bombarded with redirect ads. It pursued the issue and ended up warning one of the partners about the malicious ad code served from the platform.
Meta Refresh Tag
Other than these mentioned ways, another common method is a meta refresh tag that takes the user from one web page to another web page. In this, the bad actor sets the countdown usually invisible to the user and after the countdown ends, the user is forced to visit a web page that might contain a virus or any malware. But the good thing is almost all the most-used used browsers block the automatic redirect.
Besides, certain ads can see how the javascript is rendered and whether the users are moving their mobile phones and then, redirect them.
How to Find and Stop Forced Redirect Ads?
Here’s how forced redirect ads work and how to stop redirect ads.
Monitoring
Start by monitoring your web traffic by using tools such as Charles Proxy that dwell between the internet and your browser in order to trace the interactions while a page is loaded. Such tools are beneficial as they allow you to record the interaction between the user and the page load event along with tracing the third parties and other page redirects that are involved.
Manual On & Off
The method is quite tedious and exhaustive. If you have multiple header bidding partners, try turning off one partner at a time and monitor if the redirect ads still pop up. This would assist in knowing which header bidding partner is the reason for redirect ads. Once you have found the header bidding partner contributing to forced redirect ads, you can notify them about the situation and ask them to immediately block the buyers delivering redirect ads.
Technology
You can also make use of the ad redirect detection services. In this, the service provider executes a complete automatic search daily on the customer’s website to inspect for possible redirects. Such services assist in catching the redirects and also identifying the reasons or fraudsters behind them.
For instance, Confiant, a redirect/malware prevention company, scans ad units on your website and determines whether the ads are made to redirect users or not. However, to scan an ad unit takes 50ms. So, it might make your pages load a bit slow (depending on the number of ad units.). Still, if you want to give it a try, here’s a list of more ad fraud detection companies.
Trusted Exchanges and SSPs
The root is from the demand and when you cut down the bad actors from the supply, the volume of redirect ads will reduce to a great extent automatically. Partner with reliable ad exchanges and ensure your SSP is also following the same. After all, your SSPs are handling your demand partners.
That’s why at Automatad, we test, verify, and partner with trusted ad exchanges and DSPs to ensure quality ads. In fact, our publishers have never experienced calculable redirects before.
What About SafeFrames?
In case you’re wondering, whether SafeFrames could solve the redirecting issues, it can. But the adoption isn’t that great among the publishers.
Because SafeFrames could be a problem for third-party ad-tech vendors (such as viewability and brand safety vendors) as they can’t see what’s happening on the page when there are SafeFrames. Some older browser versions don’t even render SafeFrames and there’ll be discrepancies as the rendering will take time to complete.
But there are workarounds available to tackle the complications.
IAB said SafeFrames are updated to transact viewability data and Prebid, the most-used open source wrapper supports SafeFrames. Google Ad Exchange will automatically enable SafeFrames whenever it can. So, SafeFrames are widely in use, however, publishers are looking for a middle ground. Fox Media developed its own sandboxing code to prevent redirects and let other third parties measure without any discrepancies.
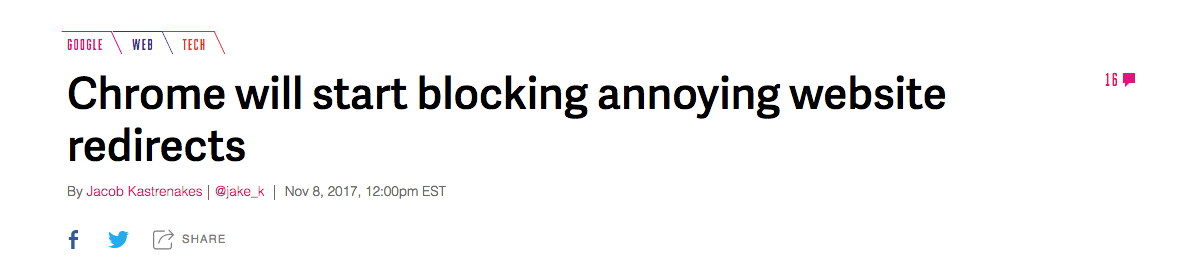
What’s Next?
Google is already blocking the ad redirects on its browser and it will continue to release updates to improve the user experience. In addition, users who’re frustrated with the redirects have installed ad blockers. The more we wait, the worse it gets. Once we start screening and blocking the forced redirect ads from the buy-side, users will eventually give up on ad blockers (of course, with the right messages and quality ads).